A group called SideCopy, which is associated with Pakistan, is using a recent security flaw in WinRAR to attack Indian government organizations. They are delivering various remote access trojans like AllaKore RAT, Ares RAT, and DRat in these attacks. SideCopy has been active since at least 2019 and is known for targeting Indian and Afghan entities. It’s believed to be a sub-group of Transparent Tribe (also known as APT36).
SideCopy and APT36 both use similar infrastructure and code to aggressively target India. In a report, SEQRITE researcher Sathwik Ram Prakki mentioned this.
In a previous incident in May, SideCopy used a phishing campaign with India’s Defence Research and Development Organization as bait to deliver malware for stealing information.
More recently, SideCopy has been involved in phishing attacks on the Indian defense sector. They use ZIP archives to spread the Action RAT and a new .NET-based trojan with 18 different commands.
The new phishing campaigns detected by SEQRITE target both Linux and Windows operating systems.
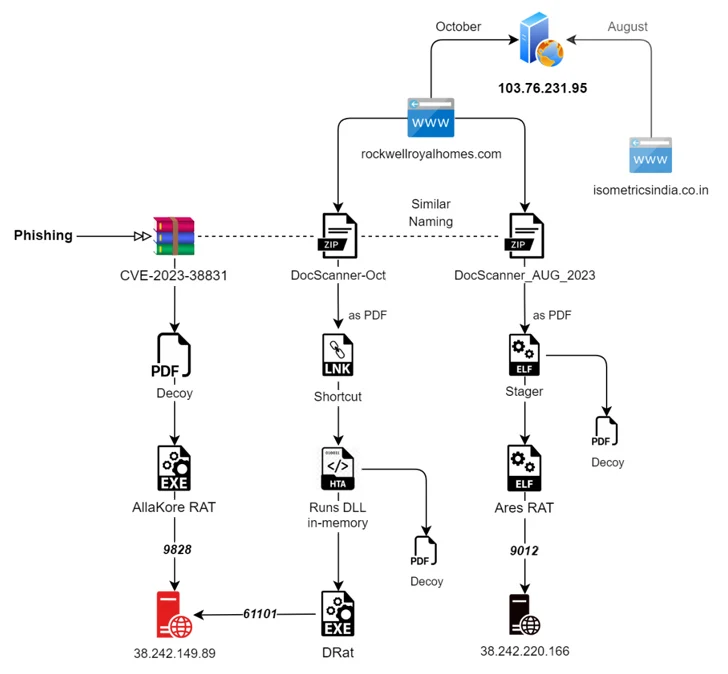
There are two separate attacks happening:
- In the first one, a Golang-based ELF binary is used to create a Linux version of Ares RAT. This RAT can do things like find files, take screenshots, and upload/download files.
- The second attack takes advantage of a security vulnerability (CVE-2023-38831) in the WinRAR tool to run malicious code. This leads to the deployment of AllaKore RAT, Ares RAT, and two new trojans called DRat and Key RAT.
AllaKore RAT can steal system info, record keystrokes, capture screenshots, transfer files, and take control of the victim’s computer to execute commands and send stolen data to a command-and-control server.
DRat can receive 13 different commands from the command-and-control server to collect system data, download and run additional programs, and manage files.
The reason they’re targeting Linux is likely because India has decided to use a Linux operating system called Maya OS in government and defense sectors instead of Microsoft Windows.
SideCopy consistently targets Indian defense organizations with various remote access trojans, and they’re using zero-day vulnerabilities. APT36, another threat group, is also adding to its Linux toolkit and sharing its Linux tools with SideCopy to deploy an open-source Python RAT called Ares.
