Security experts have uncovered a sneaky online scheme where cyber attackers use misleading Google ads to trick people who want to download genuine software like WinSCP. This dangerous activity is known as SEO#LURKER, and it’s important to stay alert.
The bad actors use a fake advertisement to send users to a compromised website called gameeweb[.]com. From there, users are redirected to a deceptive website controlled by the attackers. This website looks like the real WinSCP site, but it’s actually a trap to install malware on your device.
The attackers seem to be taking advantage of Google’s Dynamic Search Ads, which automatically create ads based on a website’s content. These ads lead unsuspecting users to the harmful site.
The attackers’ goal is to make users think they’re downloading WinSCP from a legitimate site, winccp[.]net. However, it’s a fake version designed to infect your device with malware.
The attack involves several steps. First, users are sent to the fake WinSCP site, but if they don’t have the right information, they end up redirected to a famous Rick Astley YouTube video as a joke.
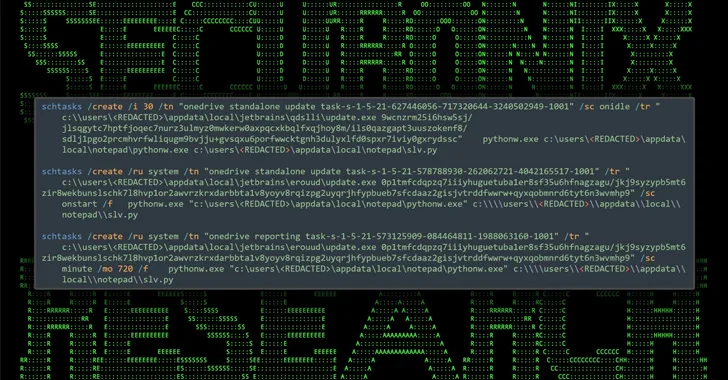
The final step includes a ZIP file (“WinSCP_v.6.1.zip”) with an executable setup. When launched, it secretly loads and runs a DLL file named python311.dll, which is hidden in the file. This DLL downloads a real WinSCP installer to make it look legitimate while also quietly activating malicious Python scripts in the background.
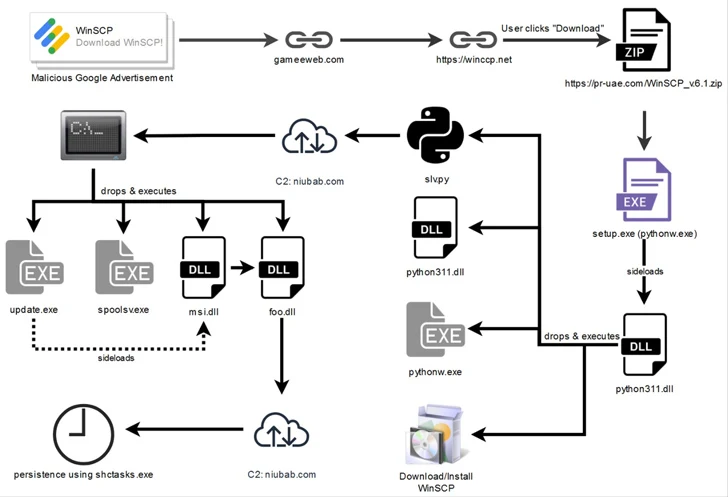
These Python scripts communicate with a server controlled by the attackers, allowing them to send further instructions to compromise the victim’s device. The researchers noted that the attack seems to target people searching for WinSCP, and those in the U.S. may be particularly affected due to geoblocking on the malware-hosting site.
This isn’t the first time Google’s Dynamic Search Ads have been misused for spreading malware. In a recent case, users searching for PyCharm were directed to a compromised website hosting a deceptive installer, leading to malware deployment.
Cybercriminals have increasingly turned to malvertising in recent years. Just last month, Malwarebytes uncovered a rise in credit card skimming campaigns that compromised hundreds of e-commerce websites. These campaigns aimed to steal financial information by injecting realistic-looking fake payment pages.
It’s crucial to stay vigilant online and be cautious when downloading software. Always ensure you are on the official website and avoid clicking on suspicious ads or links.